About Us

We are a consulting company that offers cybersecurity and privacy services, in order to protect the information assets of your company. We have specialists and experience in the industry to support the evaluation of business risks and the alignment of the Information Security strategy with the business.
Our cybersecurity and privacy methodologies are based on the best practices in the worldwide such as:
- CIBERSEGURIDAD: Swift CSP, NIST, ISO 27001, PCI DSS, EC-Council , OWASP, OSSTMM, OWASP and more.
- PRIVACy: LFPDPPP, GDPR and more.

¿Why Integrity?
We have the presence of specialists in Monterrey, as well as globally so that if necessary, have resources on site working in parallel. We have the experience and skills necessary to help companies to take preventive and reactive measures for the organizations and technological systems that allow us to protect the information in an effort to maintain confidentiality, availability and integrity of data information.
Our Services
We offer security and privacy services suited to your needs, adapted to the new cybersecurity risks that arise in the world in order to protect your data.

Information Security Assessments
Our security assessments help our clients to know the security maturity level, best practices, controls and policies of information security, as well as help compliance with regulations and audits. Security assessments are based on the following frameworks in the world: Swift CSP, ISO 27001, NIST, PCI DSS, CSA and more.

Pentesting & Vulnerability Assessment
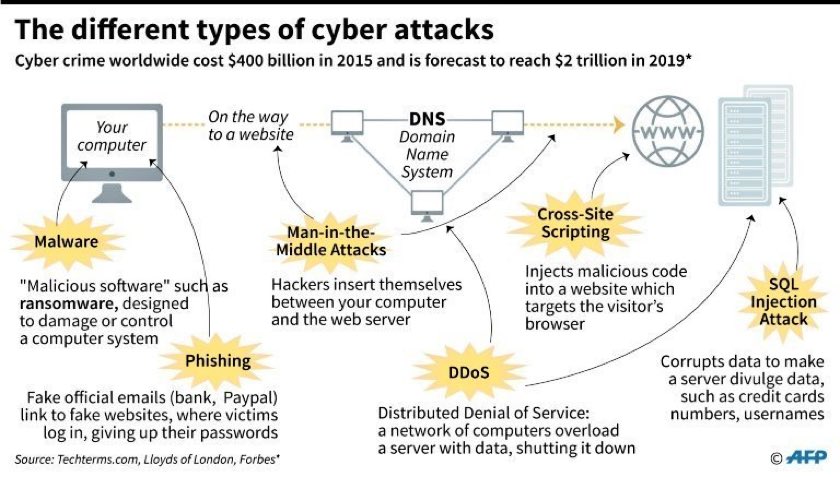
.The purpose of our penetration testing and vulnerability analysis services is to assess the security of the IT infrastructure by exploiting the weaknesses, breaches and vulnerabilities in the same way that any hacker would through the operating systems, services, applications, inappropriate configurations or behavior of the end user in your company, among the different services we offer we have:- Prescanning, Detection, Analysis and Remediation of Vulnerabilities
- Black Box Pentesting
- Gray Box Pentesting
- White Box Pentesting
- Wireless Security Testing
- Web Application testing
- Mobile Application Testing
- Social Engineering (Phishing)

Cloud Security
Integrity helps to evaluate and secure your infrastructure and data hosted in the cloud. Using the most efficient and advanced tools to perform penetration-testing in the cloud, detecting breaches and analyzing vulnerabilities. Our cloud security assessments will solve the most important questions about cloud security:
Is sensitive information protected on the internet?Are my personal data published on the internet?
Are my databases published on the internet?
Does the cloud service provider have regular external security audits?
What is your policy updates and patches for my servers in the cloud?
Do you have anti-malware or intrusion detection (IDS) products scanning my infrastructure in the cloud?
What types of authentication are available in your service?
What types of controls are available for Identity and Access Control in the accounts of your users?
Is there encryption available for traffic to and from the cloud, or storage?

Privacy & Data Protection
.Integrity puede ayudarle a evaluar cómo afecta la privacidad a su empresa e instituir un exhaustivo reglamento de privacidad informado por las ideas de los marcos globales como GDPR (Europa), LFPDPPP (México Empresas), LFPDPSO (México Gobierno), etc.2. Conduct privacy, security and/or identity theft prevention assessments & benchmarking of key controls.
3. Perform personal information inventories of the business processes and locations that handle high-risk or regulatory sensitive information.
4. Build privacy program business plans, budgets and roadmaps.
5. Design and implement solutions to address key risks and areas of noncompliance; enhance data classification scheme and technical and physical security safeguards; re-architect global data flows; design automated vendor privacy and security oversight programs.
Compliance of SWIFT Customer Security Controls Framework (CSP)
Adequate service for financial institutions that use SWIFT services for international banking transactions.
In response to a number of cyber attacks and breaches throughout 2016, SWIFT has identified 16 mandatory and 11 optional security controls for all its 11,000 customers worldwide. All customers will be asked to attest to meeting the controls, with results shared with counterparts and regulators.. Integrity helps to perform an evaluation of the current state of the controls required and recommended by the SWIFT CSP, as well as to report the result (Testimony - Self certification) of the compliance of the 27 controls in the SWIFT portal CSP Registry Security Attestation Application ( KYC-SA).


 secure@integrity.cx
secure@integrity.cx +52(844)107-5210
+52(844)107-5210

